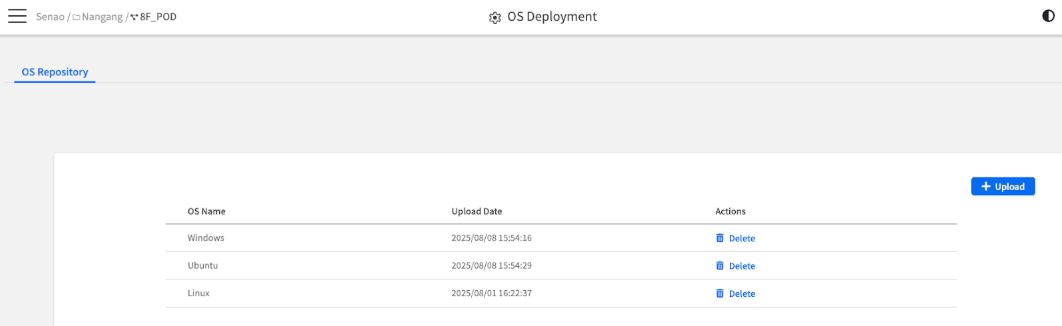
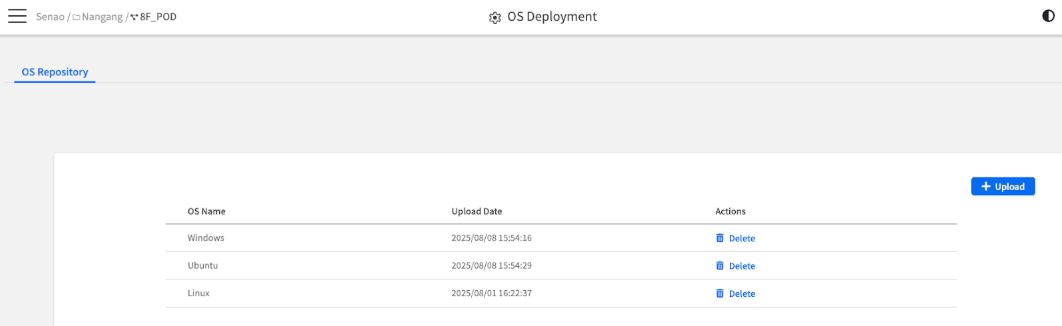
The main OS Repository interface, showing the list of uploaded ISOs and the "+ Upload" button
The main OS Repository interface, showing the list of uploaded ISOs and the "+ Upload" button
| Component | Purpose |
|---|---|
| The ISO List | The main table displays all ISOs currently available in the repository |
| The + Upload Button | Your entry point for adding new ISO images to the library |
| Column | Description & Why It Matters |
|---|---|
| OS Name | The Unique Key: This is the identifier you assign to the ISO file. It's the name you will select when mounting the image on a node. |
| Upload Date | Version Control: This timestamp helps you track when an image was last updated, which is useful for knowing if you have the latest version. |
| Actions | Management Operations: Provides the Delete button to remove the ISO from the repository. |

The OS Name selection dropdown in the Upload dialog
| Item | Verification | Notes |
|---|---|---|
| Network Connectivity | BMC can reach HTTPS File Server | Test with ping or connectivity check |
| Storage Space | Sufficient space for OS installation | Check target node storage capacity |
| Backup Strategy | Critical data backed up if needed | Document recovery procedures |
| BIOS Settings | Boot order and virtualization settings | May need adjustment via BMC |
| Scenario | Approach | Considerations |
|---|---|---|
| New Node Setup | Fresh OS installation | No data loss concerns, straightforward process |
| OS Refresh | Complete reinstallation | Backup user data, document configurations |
| Recovery Operations | Restore from known-good image | May need specific recovery ISOs |
| Testing/Development | Flexible deployment | Can use beta or specialized images |